Week Introduction
Cybersecurity is risk management under uncertainty. You cannot eliminate all threats or patch all vulnerabilities. The professional skill is prioritizing what matters most — balancing likelihood, impact, and available resources.
This week integrates concepts from Weeks 1-4 into a unified risk framework. You will learn to distinguish threats from vulnerabilities, calculate risk, and make defensible prioritization decisions.
Learning Outcomes (Week 5 Focus)
By the end of this week, you should be able to:
- LO1 - Foundational Concepts: Define and distinguish threats, vulnerabilities, and risks using precise terminology
- LO4 - Risk Reasoning: Apply risk thinking to prioritize security decisions based on likelihood, impact, and exposure
- LO8 - Integration: Connect technical vulnerabilities to business risk (synthesis across weeks)
Lesson 5.1 · Threats: Sources of Potential Harm
Definition: A threat is any circumstance or event with the potential to cause harm to a system, organization, or individual. Threats represent what could happen, not what has happened.
Threat categories (by source):
-
Adversarial threats: Intentional actors with malicious intent
Examples: Nation-state hackers, cybercriminals, hacktivists, malicious insiders
Characteristics: Strategic, adaptive, motivated by specific goals (money, espionage, disruption) -
Accidental threats: Human error without malicious intent
Examples: Employee misconfigures cloud storage, admin deletes production database
Characteristics: Common, often preventable with training and controls -
Environmental threats: Natural events or infrastructure failures
Examples: Power outages, floods, fires, hardware failures
Characteristics: Unpredictable timing, require business continuity planning -
Structural threats: Inherent system design flaws
Examples: Software bugs, protocol weaknesses, architectural assumptions
Characteristics: Exist regardless of attacker presence, discovered over time
Threats exist independently of vulnerabilities. A nation-state hacking group (threat) exists whether your systems are vulnerable or not. Risk emerges when threat meets vulnerability.
Threat modeling questions:
- Who or what could cause harm? (Threat actor identification)
- What are they capable of? (Technical skill, resources, access)
- What motivates them? (Financial gain, espionage, ideology, accident)
- How likely are they to target this system? (Attractiveness, exposure)
Lesson 5.2 · Vulnerabilities: Exploitable Weaknesses
Definition: A vulnerability is a weakness in a system that could be exploited to cause harm. Vulnerabilities represent how harm could occur.
Vulnerability categories (by type):
-
Technical vulnerabilities: Flaws in software, hardware, or protocols
Examples: Buffer overflows, SQL injection, unpatched systems, weak encryption
Common Weakness Enumeration (CWE): Standardized list of software vulnerability types -
Configuration vulnerabilities: Insecure system settings
Examples: Default passwords, open ports, excessive permissions, missing encryption
Note: Often easier to exploit than code-level bugs (no 0-day needed) -
Operational vulnerabilities: Process and procedure weaknesses
Examples: No patch management, weak access reviews, missing monitoring, poor incident response
Impact: Enable attacks to persist undetected -
Human vulnerabilities: Social engineering susceptibility
Examples: Phishing success, credential reuse, insider threats (intentional or accidental)
Reality: Humans are often the weakest link in technical systems
Critical distinction: Vulnerability ≠ Risk
A vulnerability in isolation is just a weakness. It becomes a risk only when:
- A credible threat could exploit it (threat + vulnerability)
- Exploitation would cause meaningful harm (impact)
- The system is accessible to the threat (exposure)
Example: A web server has an unpatched critical vulnerability (CVE). Risk depends on:
- Is it internet-facing? (Exposure — high if public, low if internal-only)
- Is there a public exploit? (Threat capability — high if weaponized)
- What data does it protect? (Impact — high if customer PII, low if test environment)
Defender takeaway: Prioritize vulnerabilities based on exploitability, exposure, and impact — not just severity score. A "critical" CVE in an offline system may be lower priority than a "medium" CVE in an internet-facing payment processor.
Lesson 5.3 · Risk: The Intersection of Threat, Vulnerability, and Impact
Definition: Risk is the potential for loss or harm when a threat exploits a vulnerability. It is calculated as a function of likelihood and impact.
Risk formula (conceptual):
Risk = Likelihood × Impact

Where:
-
Likelihood: Probability that threat will exploit vulnerability
Factors: Threat capability, vulnerability exploitability, exposure, existing controls -
Impact: Magnitude of harm if exploitation succeeds
Factors: Asset value, business criticality, data sensitivity, regulatory consequences
Risk matrix (qualitative approach):
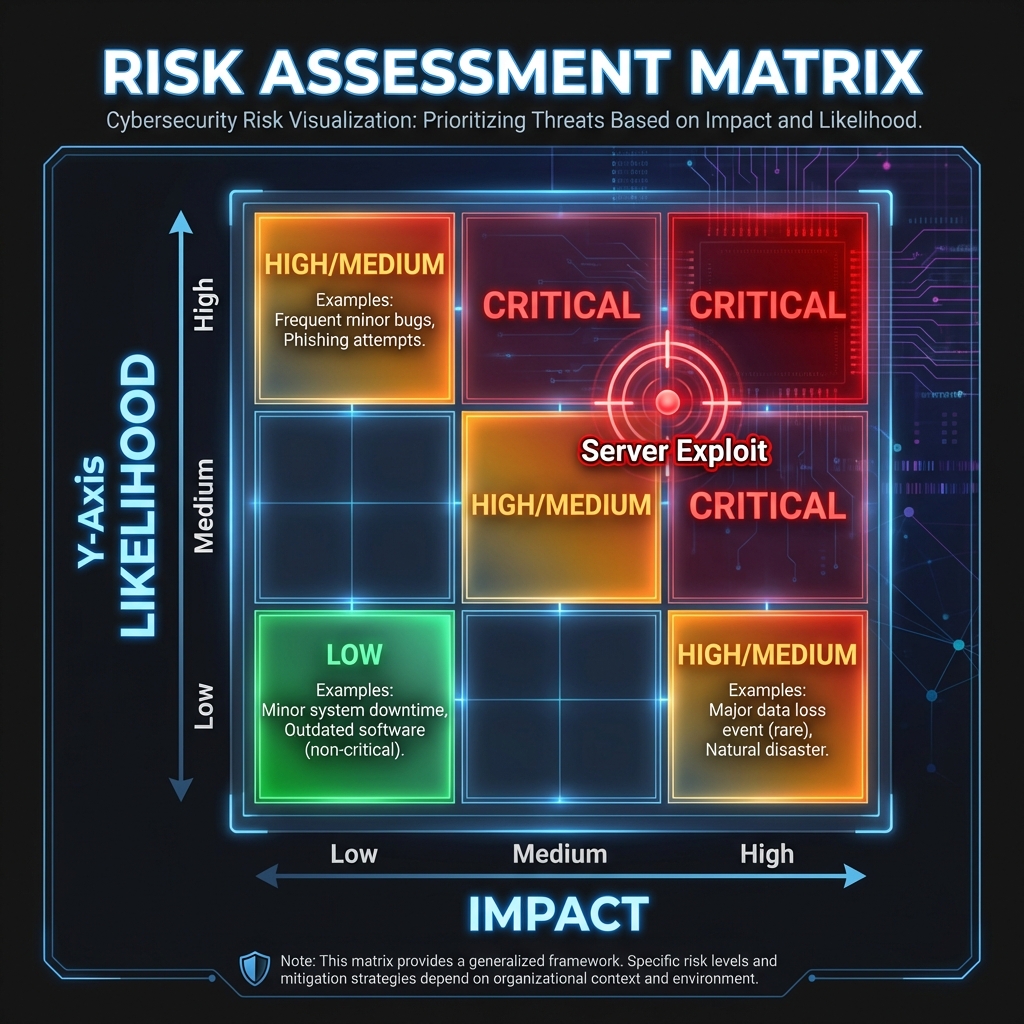
Example risk scenarios:
Example risk scenarios:
- Critical Risk: Internet-facing payment server with known RCE exploit (high likelihood) + stores credit card data (high impact) = Patch immediately
- Medium Risk: Internal dev server with XSS vulnerability (medium likelihood — requires authenticated insider) + contains test data only (low impact) = Schedule fix, not emergency
- Low Risk: Air-gapped system with buffer overflow (zero likelihood — no network access) + non-critical data (low impact) = Defer until next maintenance window
Key insight: Risk is contextual
The same vulnerability has different risk levels in different contexts. A SQL injection flaw is:
- Critical risk in production customer database
- Medium risk in internal employee directory
- Low risk in isolated test environment with no real data
Lesson 5.4 · Vulnerability Prioritization: Risk-Based Approach
Reality check: Organizations have thousands of known vulnerabilities. Attempting to fix them all wastes resources and delays fixing what actually matters.
Common mistake: CVSS score-based prioritization
Many organizations patch "critical" CVEs (CVSS 9.0+) first, regardless of context. This ignores exposure and impact:
- CVSS 9.8 in offline backup system = Low actual risk
- CVSS 6.5 in internet-facing authentication = High actual risk
Better approach: Risk-based prioritization
Prioritize based on the intersection of:
-
Exploitability:
- Is exploit code publicly available? (Weaponized CVEs are highest priority)
- Is it being actively exploited in the wild? (Threat intelligence feeds)
- How difficult is exploitation? (Authentication required? Physical access needed?)
-
Exposure:
- Is the vulnerable system internet-facing? (External > Internal)
- Who can reach it? (Anyone > Authenticated users > Admins only)
- Is it segmented from critical assets? (Blast radius analysis)
-
Impact:
- What data is at risk? (Customer PII > Employee data > Test data)
- What business function depends on it? (Revenue-generating > Support systems)
- Are there regulatory consequences? (HIPAA, PCI-DSS, GDPR fines)
Prioritization tiers:
- Tier 1 (Patch immediately): Internet-facing + weaponized exploit + high-value data
- Tier 2 (Patch this sprint): Internal systems + known exploit + medium impact
- Tier 3 (Schedule for next quarter): Low exposure + theoretical vulnerability + low impact
- Tier 4 (Accept risk): Air-gapped + no exploit + negligible impact
Real-world example: Equifax breach (2017)
Equifax had a known Apache Struts vulnerability (CVE-2017-5638) for months. It should have been Tier 1 priority:
- ✅ Internet-facing web application (maximum exposure)
- ✅ Public exploit code available within days (weaponized)
- ✅ Protected access to 143 million consumer records (catastrophic impact)
Failure to prioritize correctly = $700M+ in costs, reputational destruction, CEO resignation.
Lesson 5.5 · Risk Treatment: Accept, Mitigate, Transfer, Avoid
Core principle: You cannot eliminate all risk. Organizations must decide how to respond to each identified risk based on tolerance, resources, and business objectives.
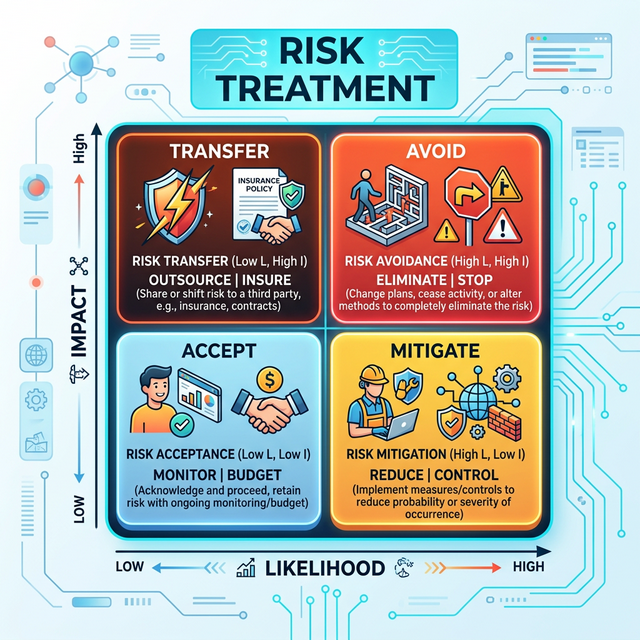
Four risk treatment strategies:
-
Mitigate (Reduce): Apply controls to lower likelihood or impact
Example: Patch vulnerability, implement MFA, deploy firewall
When to use: Risk exceeds tolerance, mitigation is cost-effective -
Accept (Tolerate): Acknowledge risk but take no action
Example: Low-impact vulnerability in legacy system being retired next quarter
When to use: Risk is within tolerance, cost of mitigation exceeds benefit
Critical: Must be explicit, documented decision (not negligence) -
Transfer (Share): Shift financial impact to third party
Example: Cyber insurance, outsource to managed security provider, cloud provider SLA
When to use: Cannot fully mitigate, want financial protection
Note: Transfers financial risk, not reputational or legal risk -
Avoid (Eliminate): Remove the risky activity entirely
Example: Decommission internet-facing system, discontinue risky service, block entire country
When to use: Risk cannot be mitigated to acceptable level, activity is non-essential
Decision framework:
For each identified risk, ask:
- Is this risk within our tolerance? (If yes → Accept; if no → continue)
- Can we eliminate the activity? (If yes and non-essential → Avoid; if no → continue)
- Can we mitigate to acceptable level? (If yes and cost-effective → Mitigate; if no → continue)
- Should we transfer financial impact? (If yes → Transfer; if no → re-evaluate tolerance or accept residual risk)
Residual risk: Risk that remains after controls are applied. All mitigation leaves some residual risk — perfect security is impossible. Organizations must explicitly accept residual risk.
Self-Check Questions (Test Your Understanding)
Answer these in your own words (2-3 sentences each):
- What is the difference between a threat and a vulnerability? Can you have one without the other?
- Explain the risk formula (Risk = Likelihood × Impact). Why do both factors matter?
- Why is CVSS score alone insufficient for vulnerability prioritization? Give one example.
- What does it mean to "accept" a risk? When is this appropriate vs negligent?
- You find a critical vulnerability in a system. Walk through the decision framework: What questions would you ask before choosing a risk treatment strategy?
Lab 5 · Risk Assessment and Prioritization
Time estimate: 40-50 minutes
Objective: Conduct a structured risk assessment on a real system. You will identify threats and vulnerabilities, calculate risk, prioritize findings, and recommend treatment strategies with defensible justification.
Step 1: Choose Your System (5 minutes)
Select one system from this list (or propose your own with similar complexity):
- E-commerce website: Public storefront, payment processing, customer database
- University learning management system: Student grades, assignment submissions, instructor accounts
- Healthcare patient portal: Medical records, appointment scheduling, prescription requests
- Financial services app: Account balances, transfers, investment portfolios
- Corporate email system: Internal communications, calendar, file attachments
Why it matters: Risk is contextual — same vulnerability has different risk in different systems.
Step 2: Identify Assets and Their Value (10 minutes)
List at least 3 critical assets the system protects:
- Asset name: (e.g., "customer credit card data," "student grades," "patient medical records")
- CIA priority: Which matters most — Confidentiality, Integrity, or Availability?
- Business impact if compromised: Financial loss, regulatory fines, reputational damage, legal liability
Example for healthcare portal:
-
Asset: Patient medical records
CIA priority: Confidentiality (HIPAA compliance)
Impact: $50K+ per record fine, class action lawsuits, loss of patient trust -
Asset: Prescription authorization system
CIA priority: Integrity (wrong medication could be fatal)
Impact: Patient harm, malpractice liability, regulatory sanctions -
Asset: Appointment scheduling
CIA priority: Availability (patients need timely access)
Impact: Patient dissatisfaction, operational disruption, revenue loss
Step 3: Identify Threats (10 minutes)
For each asset, identify at least one credible threat:
- Threat actor: Who/what? (External attacker, insider, accident, system failure)
- Motivation: Why would they target this? (Financial gain, espionage, vandalism, none if accidental)
- Capability: What resources do they have? (Script kiddie, organized crime, nation-state)
Example threats for healthcare portal:
-
Threat to medical records: Cybercriminal group seeking to sell patient data on
dark web
Motivation: Financial (medical records worth $50-250 each)
Capability: Medium-high (organized, use ransomware + data exfiltration) -
Threat to prescriptions: Malicious insider (employee) altering records for drug
trafficking
Motivation: Financial (opioid black market)
Capability: High (authorized access, knows system)
Step 4: Identify Vulnerabilities (10 minutes)
For each threat, identify one vulnerability they could exploit:
- Vulnerability type: Technical, configuration, operational, or human
- Specific weakness: What exactly is exploitable?
- How threat exploits it: Attack method
Example vulnerabilities:
-
Vulnerability for data theft: Web application SQL injection (CWE-89)
Type: Technical
Exploitation: Attacker injects malicious SQL, extracts entire patient database -
Vulnerability for insider threat: No access logging or monitoring on
prescription system
Type: Operational
Exploitation: Insider changes prescriptions, no audit trail to detect unauthorized modifications
Step 5: Calculate Risk (10 minutes)
For each threat/vulnerability pair, assess risk using the matrix from Lesson 5.3:
-
Likelihood: Low / Medium / High
Consider: Threat capability, vulnerability exploitability, existing controls, exposure -
Impact: Low / Medium / High
Consider: Asset value, business criticality, regulatory consequences - Overall Risk: Use matrix to determine (Low / Medium / High / Critical)
Example risk calculation:
-
Scenario 1: SQL injection → data breach
Likelihood: High (public exploit available, system internet-facing, no WAF)
Impact: High ($50K+ per record fines, class action lawsuits)
Risk: Critical (High × High) -
Scenario 2: Insider prescription tampering
Likelihood: Medium (requires malicious employee, some access controls exist)
Impact: High (patient harm, malpractice liability)
Risk: High (Medium × High)
Step 6: Prioritize and Recommend Treatment (5 minutes)
Rank your identified risks from highest to lowest, then propose treatment for the top risk:
- Risk ranking: List in priority order (Critical → High → Medium → Low)
- Treatment strategy: Mitigate, Accept, Transfer, or Avoid?
- Specific controls: What would you implement? (Be concrete, not generic)
- Justification: Why this treatment? Why this priority?
Example treatment plan:
-
Top priority: SQL injection risk (Critical)
Treatment: Mitigate
Controls:- Immediate: Deploy web application firewall (WAF) with SQL injection rules
- Short-term: Code review + parameterized queries (fix root cause)
- Ongoing: Penetration testing quarterly, static code analysis in CI/CD
Justification: Critical risk, cost-effective mitigation available, regulatory requirement (HIPAA) -
Second priority: Insider prescription tampering (High)
Treatment: Mitigate
Controls:- Implement audit logging on all prescription changes (who, what, when)
- Require dual authorization for high-risk medication changes
- Anomaly detection alerts for unusual prescription patterns
Justification: High impact (patient safety), medium likelihood, detective controls cost-effective
Success Criteria (What "Good" Looks Like)
Your lab is successful if you:
- ✅ Identified assets with clear CIA priorities and business impact
- ✅ Matched credible threats to realistic vulnerabilities
- ✅ Calculated risk using likelihood × impact (not just severity scores)
- ✅ Prioritized risks in defensible order (not arbitrary)
- ✅ Proposed concrete, actionable controls (not "improve security")
- ✅ Justified decisions with business reasoning (cost, impact, compliance)
Extension (For Advanced Students)
If you finish early, explore these questions:
- What is residual risk after your proposed controls? Would you accept it or add more controls?
- How would you measure effectiveness of your controls? (Metrics, KPIs)
- If budget only allowed implementing ONE control, which would you choose and why?
🎯 Hands-On Labs (Free & Essential)
Apply threat, vulnerability, and risk thinking with beginner-friendly labs. Complete these before moving to reading resources.
🎮 TryHackMe: Security Principles
What you'll do: Work through core security principles like least privilege, defense in
depth, and risk-based decision making.
Why it matters: This lab turns abstract risk concepts into concrete security
choices you'll make throughout the degree.
Time estimate: 1-1.5 hours
🎮 TryHackMe: OWASP Top 10 (Intro)
What you'll do: Explore real-world vulnerability categories and how they map to risk
(likelihood x impact).
Why it matters: Vulnerability awareness makes risk assessment realistic instead of
theoretical.
Time estimate: 1.5-2 hours
🏁 PicoCTF Practice: Web Exploitation (Beginner)
What you'll do: Attempt beginner web challenges that highlight common vulnerabilities
and their impact.
Why it matters: Seeing vulnerabilities firsthand makes it easier to prioritize real
risk over hypothetical risk.
Time estimate: 1-2 hours
💡 Lab Tip: Keep a simple risk table: vulnerability, likelihood, impact, and priority. You'll reuse this structure throughout your degree.
Resources (Free + Authoritative)
Work through these in order. Focus on risk reasoning frameworks.
📘 NIST SP 800-30 - Guide for Conducting Risk Assessments
What to read: Chapter 2 "The Fundamentals" (pages 7-21) — definitions of
threat, vulnerability, risk.
Why it matters: Authoritative framework used by governments and
enterprises. Teaches structured risk thinking.
Time estimate: 30 minutes (skim examples, focus on concepts)
📘 OWASP Threat Modeling
What to read: Introduction and "Getting Started" sections.
Why it matters: Practical guide to identifying threats before systems are
built. Used in secure development.
Time estimate: 20 minutes
📘 FIRST CVSS Calculator - Understanding Vulnerability Scoring
What to explore: Use the interactive calculator to score a few example
vulnerabilities (pick from recent CVEs).
Why it matters: Understand what CVSS measures (and what it doesn't —
context, exposure, business impact).
Time estimate: 15 minutes
📘 Cloudflare Learning - What is Defense-in-Depth?
What to read: Entire article on layered security approach.
Why it matters: Connects risk mitigation to practical control design. No
single control is perfect.
Time estimate: 10 minutes
Tip: Completion and XP persist via localStorage. If progress doesn't update immediately, refresh once.
Weekly Reflection Prompt
Aligned to LO4 (Risk Reasoning) and LO8 (Integration)
Write 200-300 words answering this prompt:
Using your Lab 5 risk assessment, explain how you prioritized risks. Why did you choose to address certain vulnerabilities before others?
In your answer, include:
- How you calculated risk (likelihood × impact) for at least two scenarios
- Why CVSS score alone would have been insufficient for prioritization
- What factors influenced your treatment decision (mitigate vs accept vs transfer vs avoid)
- How you balanced security improvement against cost and business constraints
- What "residual risk" means in your context and whether you would accept it
What good looks like: You explain the reasoning process, not just the outcome. You show understanding that risk is contextual — same vulnerability has different priority in different systems. You demonstrate professional judgment: balancing perfect security (impossible) against acceptable risk (realistic).