Week Introduction
Security is adversarial — there are people actively trying to break what you build. Understanding attacker psychology, capabilities, and constraints is as important as understanding technology.
This week explores the human dimension of cybersecurity: who attacks systems, why they do it, what defenders are up against, and why defense is fundamentally asymmetric (attackers only need to succeed once; defenders must succeed continuously).
Learning Outcomes (Week 6 Focus)
By the end of this week, you should be able to:
- LO3 - Threat Landscape: Categorize threat actors by capability, motivation, and typical attack patterns
- LO4 - Risk Reasoning: Explain why attacker motivation determines attack style and target selection
- LO8 - Integration: Connect technical vulnerabilities to attacker incentives (why certain flaws get exploited)
Lesson 6.1 · Threat Actor Taxonomy: Who Attacks and Why
Core insight: "The attacker" is not one person or group. Threat actors range from opportunistic script kiddies to sophisticated nation-states. Understanding who you're defending against shapes what controls you implement.

Threat actor categories (by motivation and capability):
-
1. Script Kiddies / Opportunistic Attackers
Motivation: Fame, curiosity, boredom
Capability: Low — use pre-built tools, exploit known vulnerabilities
Target selection: Indiscriminate scanning for low-hanging fruit
Attack style: Automated, noisy, easily detected
Example: Running Shodan searches for exposed databases, using Metasploit against unpatched systems -
2. Cybercriminals (Organized Crime)
Motivation: Financial gain (primary driver)
Capability: Medium to High — sophisticated tooling, division of labor (ransomware-as-a-service)
Target selection: ROI-driven — profitable targets (payment systems, customer databases)
Attack style: Efficient, scalable, business-like operations
Example: Ransomware gangs (Conti, LockBit), credit card fraud rings, business email compromise (BEC) -
3. Hacktivists
Motivation: Political/social ideology, protest, awareness
Capability: Low to Medium — varies widely (Anonymous vs sophisticated groups)
Target selection: Symbolic — organizations representing opposed values
Attack style: Public, disruptive (DDoS, defacement, data leaks for exposure)
Example: Anonymous attacks on government sites, environmental activist breaches of energy companies -
4. Insiders (Malicious or Negligent)
Motivation: Financial (sell data), revenge (disgruntled employee), negligence (accidental)
Capability: High — authorized access, knows systems intimately
Target selection: Opportunity-based — access determines targets
Attack style: Quiet, leverages legitimate credentials, hardest to detect
Example: Edward Snowden (ideological), Tesla employee sabotage, accidental S3 bucket exposure -
5. Nation-State / APT (Advanced Persistent Threat)
Motivation: Espionage, strategic advantage, critical infrastructure disruption
Capability: Very High — zero-days, custom malware, unlimited resources
Target selection: Strategic — government, defense, critical infrastructure, intellectual property
Attack style: Stealthy, patient (persistent for months/years), sophisticated evasion
Example: APT28 (Russia), APT29 (Cozy Bear), Lazarus Group (North Korea), Chinese APTs (IP theft)
Reality check on frequency:
Despite media focus on sophisticated attacks, most breaches involve:
- Financially-motivated cybercriminals (70%+)
- Exploiting known, unpatched vulnerabilities (not zero-days)
- Phishing / credential theft (easiest path in)
- Opportunistic targeting (automated scanning finds you)
Defender implication: Design defenses for the threats you'll actually face (opportunistic criminals), not just the ones that make headlines (nation-states).
Lesson 6.2 · Why Attackers Win: The Path of Least Resistance
Core principle: Attackers don't need to be brilliant — they need to be more patient and thorough than defenders. They look for the weakest link, not the strongest challenge.
Why most attacks succeed (ranked by frequency):
-
Unpatched known vulnerabilities (35-40% of breaches)
Attackers scan for CVEs with public exploits, find unpatched systems
Example: Equifax (Apache Struts), WannaCry (EternalBlue)
Defender failure: Patch management breakdown -
Stolen or weak credentials (30-35% of breaches)
Phishing, password reuse, credential stuffing, default passwords
Example: Target breach (HVAC vendor credentials), Colonial Pipeline (compromised VPN password)
Defender failure: Weak authentication, no MFA -
Misconfigured systems (15-20% of breaches)
Open S3 buckets, exposed databases, overly permissive firewall rules
Example: Capital One (misconfigured AWS WAF), MongoDB instances exposed on internet
Defender failure: Configuration management, default-deny policies -
Social engineering (10-15% of initial access)
Manipulating humans to bypass technical controls
Example: Twitter Bitcoin scam (phone spear-phishing of employees), Uber breach (contractor compromise)
Defender failure: Security awareness, verification procedures
Key insight: Sophistication is rare
Zero-day exploits and custom malware make headlines, but represent less than 5% of attacks. Most attackers use:
- Publicly available tools (Metasploit, Cobalt Strike, off-the-shelf ransomware)
- Known techniques (MITRE ATT&CK documents common tactics)
- Automated scanning (Shodan, Censys, mass vulnerability scanners)
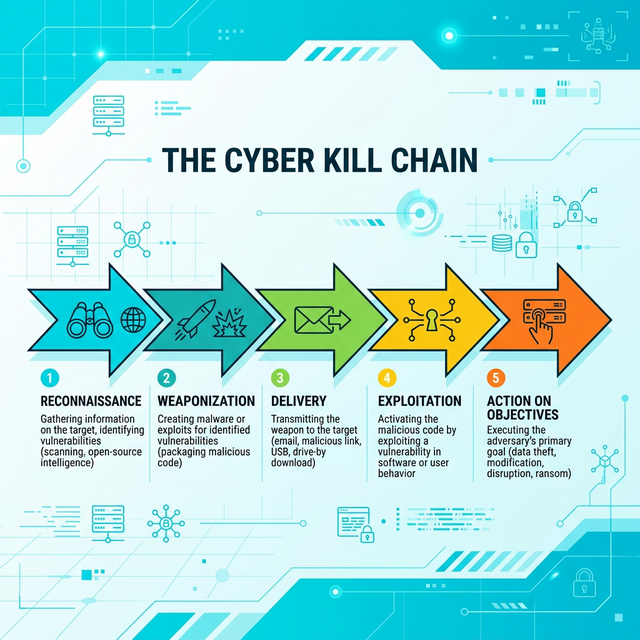
The attack kill chain (simplified):
- Reconnaissance: Scan for vulnerable systems (automated, low-effort)
- Initial access: Exploit vulnerability or stolen credential (easiest weakness)
- Establish foothold: Install backdoor, create persistence
- Lateral movement: Move from initial system to valuable targets
- Achieve objective: Steal data, deploy ransomware, disrupt operations
Defender reality check:
Attackers succeed not because defenders lack sophisticated tools, but because:
- Basic hygiene fails (patching, MFA, monitoring)
- Complexity creates gaps (shadow IT, forgotten systems)
- Human error is inevitable (click phishing link, misconfigure cloud)
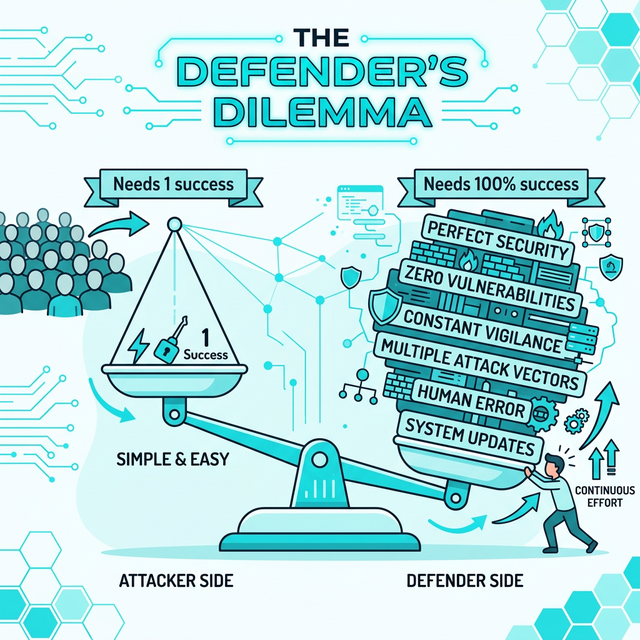
- Defenders must protect everything; attackers need only one way in
Lesson 6.3 · The Defender's Dilemma: Asymmetric Warfare
Fundamental asymmetry: Attackers only need to find one weakness. Defenders must protect against all possible attacks, all the time, while keeping systems functional for legitimate users.
Constraints defenders face (that attackers don't):
-
1. Must maintain usability
Perfect security = completely locked-down system = unusable
Example: Can't require biometric scan + hardware token + manager approval for every email
Trade-off: Convenience vs security (business always needs some of both) -
2. Resource constraints (budget, time, people)
Security competes with product development, sales, operations
Example: Can't patch during business hours (causes downtime), limited security staff
Reality: Must prioritize — can't fix everything, can't monitor everything -
3. Compliance and policy requirements
Must follow regulations (GDPR, HIPAA, PCI-DSS), internal policies
Example: Can't just block all USB drives (employees need them), can't ban email attachments
Constraint: Legal/regulatory boundaries limit defensive options -
4. Unknown attack surface
Shadow IT, forgotten systems, third-party dependencies
Example: Marketing department uses unapproved SaaS tool, inherited legacy systems from merger
Challenge: Can't defend what you don't know exists -
5. Must defend against all threats simultaneously
Ransomware, phishing, DDoS, insider threats, supply chain attacks, etc.
Example: While hardening web servers, attackers phish credentials; while responding to incident, new CVE drops
Reality: Constant triage, never "done"
Attacker advantages:
- Initiative: Choose when, where, and how to attack (element of surprise)
- Focus: Can dedicate 100% effort to breaking one thing
- No rules: Not constrained by business needs, ethics, or laws
- Anonymity: Can operate from anywhere, hide identity
- Time: Can wait months for perfect opportunity (defenders work 24/7)
Why defense is still possible:
Despite asymmetry, defenders can succeed by:
- Raising attacker cost: Make attacks expensive/time-consuming (defense-in-depth)
- Reducing dwell time: Detect quickly, limit damage (assume breach)
- Sharing intelligence: Learn from others' incidents (threat feeds, ISACs)
- Prioritizing ruthlessly: Protect crown jewels, accept risk elsewhere
- Building resilience: Design for graceful degradation and recovery
Mindset shift: From "prevent all attacks" to "make attacks not worth the effort and recover quickly when they succeed."
Lesson 6.4 · Motivation Determines Attack Pattern
Core insight: If you understand why an attacker wants something, you can predict how they'll try to get it. Motivation drives tactics, which informs defensive priorities.
Motivation → Attack pattern mapping:
-
Financial motivation (cybercriminals)
Attack style: Fast, scalable, high-volume
Tactics: Ransomware, credential theft, business email compromise, cryptomining
Target selection: Anyone with money/valuable data (opportunistic)
Defender focus: Rapid detection, backups, MFA, email security
Example: REvil ransomware gang — automated deployment, demand ransom, move to next victim -
Espionage motivation (nation-states, competitors)
Attack style: Slow, stealthy, persistent
Tactics: Spear-phishing, zero-days, custom malware, living-off-the-land techniques
Target selection: Strategic (government, defense contractors, R&D departments)
Defender focus: Network segmentation, anomaly detection, insider threat programs
Example: APT29 (Cozy Bear) — remain undetected for months, exfiltrate IP slowly -
Ideological motivation (hacktivists)
Attack style: Public, disruptive, symbolic
Tactics: DDoS, website defacement, data leaks for publicity
Target selection: Organizations opposing attacker's values
Defender focus: DDoS mitigation, public relations preparedness, web application hardening
Example: Anonymous — deface website with political message, leak documents to press -
Insider motivation (revenge, financial, negligence)
Attack style: Leverages legitimate access, hard to distinguish from normal activity
Tactics: Data exfiltration, sabotage, privilege abuse
Target selection: Systems they already access
Defender focus: Access logging, behavioral analytics, least privilege, exit procedures
Example: Tesla employee — modify production code for sabotage or steal IP before leaving
Why this matters for threat modeling:
When assessing risk, ask:
- What would each attacker type want from this system? (Assets of interest)
- How would they likely attack? (Tactics based on motivation)
- What defenses match the threat? (DDoS protection for hacktivists vs insider monitoring for employees)
Example: Healthcare organization threat model
- Cybercriminals: Want patient data to sell → Deploy ransomware → Prioritize backups, email filtering, endpoint protection
- Insiders: Access medical records for identity theft → Abuse legitimate credentials → Prioritize access logging, anomaly detection
- Nation-states: Unlikely unless research hospital with biotech IP → If targeted, need network segmentation, threat hunting
Lesson 6.5 · Defense as Resilience, Not Perfection
Mindset shift: The goal is not to prevent every attack (impossible). The goal is to make attacks costly enough that most attackers choose easier targets, and to recover quickly when attacks succeed.
Resilience framework (NIST Cybersecurity Framework):
-
Identify: Know what you're protecting (assets, threats,
vulnerabilities)
Why it matters: Can't defend what you don't know exists -
Protect: Implement safeguards (access control, encryption, patching)
Why it matters: Raise attacker cost, reduce likelihood -
Detect: Monitor for security events (SIEM, IDS, logging)
Why it matters: Assume breach, find attackers before damage escalates -
Respond: Contain and eradicate threats (incident response plan)
Why it matters: Minimize dwell time, limit blast radius -
Recover: Restore capabilities (backups, business continuity)
Why it matters: Return to operations quickly, learn from incidents
Mature security programs focus on:
- Mean Time to Detect (MTTD): How quickly do we notice attacks? (Goal: minutes to hours, not months)
- Mean Time to Respond (MTTR): How quickly do we contain/remediate? (Goal: hours, not days)
- Recovery Point Objective (RPO): How much data can we afford to lose? (Drive backup strategy)
- Recovery Time Objective (RTO): How quickly must we restore operations? (Drive redundancy investment)
Why "assume breach" is realistic:
- Attackers have time, resources, and initiative
- New vulnerabilities discovered daily (zero-days exist)
- Human error is inevitable (phishing will occasionally succeed)
- Supply chain introduces dependencies you can't fully control
Therefore: Design systems expecting compromise. Segment networks. Log everything. Test recovery. Build organizational muscle memory through drills.
Self-Check Questions (Test Your Understanding)
Answer these in your own words (2-3 sentences each):
- What is the difference between a script kiddie and a nation-state APT? How do their attack styles differ?
- Explain the defender's dilemma. Why do attackers have inherent advantages?
- How does attacker motivation (financial vs espionage vs ideology) shape their tactics? Give one example.
- Why is "assume breach" a more realistic security posture than "prevent all attacks"?
- What does it mean to build security resilience? Connect to the NIST framework (Identify, Protect, Detect, Respond, Recover).
Lab 6 · Threat Actor Analysis and Defensive Prioritization
Time estimate: 40-50 minutes
Objective: Analyze a system from multiple threat actor perspectives. You will identify what different attackers want, how they'd attack, and how to prioritize defenses based on realistic threat assessment.
Step 1: Choose Your System (5 minutes)
Select one system (you may reuse from previous labs or choose new):
- E-commerce platform: Customer accounts, payment processing, order history
- Social media platform: User profiles, private messages, content feeds
- Healthcare portal: Medical records, prescriptions, appointment scheduling
- Corporate email system: Internal communications, calendar, file sharing
- Financial trading platform: Account balances, transaction history, trading algorithms
Why it matters: Different threat actors target the same system for different reasons.
Step 2: Identify High-Value Assets (10 minutes)
List at least 3 assets attackers might want:
- Asset name: (e.g., "customer credit card data," "proprietary trading algorithms")
- Value to attackers: Why would they want it? (Sell on dark web, competitive advantage, blackmail)
- Value to organization: What's the business impact if compromised?
Example for e-commerce platform:
-
Asset: Payment card data (PAN, CVV, cardholder names)
Attacker value: $5-50 per card on dark web (financial motivation)
Business impact: PCI-DSS fines, class action lawsuits, loss of merchant account -
Asset: Customer login credentials (emails + passwords)
Attacker value: Credential stuffing attacks on other sites, account takeover
Business impact: Reputational damage, customer churn, regulatory fines -
Asset: Order history and browsing behavior
Attacker value: Market research, competitive intelligence
Business impact: Loss of competitive advantage, privacy violations
Step 3: Map Threat Actors to Assets (15 minutes)
For each asset, identify which threat actor type would target it and how:
| Asset | Threat Actor | Motivation | Likely Attack Method |
|---|---|---|---|
| Payment card data | Cybercriminals | Financial (sell data) | SQL injection, web app exploit, phishing admins |
| Customer credentials | Opportunistic attackers | Credential stuffing other sites | Database breach, password reuse exploitation |
| Proprietary algorithms | Competitors / APTs | Competitive advantage | Insider recruitment, spear-phishing engineers |
Create your own table matching assets to realistic threat actors.
Step 4: Assess Likelihood by Threat Actor (10 minutes)
For each threat actor, rate the likelihood they would target your system:
- High: System is attractive target with high exposure (internet-facing, valuable data)
- Medium: Some value but lower exposure or requires more effort
- Low: Unlikely target (limited value, low profile, strong defenses)
Example likelihood assessment for e-commerce:
- Cybercriminals: High — Payment data is lucrative, systems are internet-facing, automated tools available
- Nation-state APTs: Low — E-commerce has no strategic value unless selling to government/defense
- Hacktivists: Low — Unless company involved in controversial industry (fossil fuels, weapons)
- Insiders: Medium — Employees have access, financial motivation exists, but controls deter most
Step 5: Prioritize Defenses Based on Threat Assessment (10 minutes)
Based on your threat actor analysis, prioritize defensive investments:
- Top priority (address immediately): Defenses against most likely AND highest impact threats
- Medium priority (address this quarter): Defenses against medium likelihood threats or lower impact
- Low priority (monitor but defer): Defenses against unlikely threats
Example prioritization:
-
Priority 1: Defend against cybercriminals (High likelihood, High impact)
Controls: Web application firewall, input validation, PCI-DSS compliance, penetration testing
Justification: Most likely threat, catastrophic impact (card data breach) -
Priority 2: Insider threat detection (Medium likelihood, High impact)
Controls: Access logging, anomaly detection, least privilege, background checks
Justification: Lower likelihood but still significant impact -
Priority 3: APT defenses (Low likelihood, but catastrophic if targeted)
Controls: Network segmentation, threat hunting (if resources allow)
Justification: Unlikely for typical e-commerce, defer unless strategic target
Step 6: Synthesis (5 minutes)
Write a short paragraph (3-5 sentences) answering:
"How does understanding attacker motivation change your defensive strategy? Why would defending against 'all threats equally' be wasteful?"
Example answer:
Understanding attacker motivation allows prioritization based on realistic threats rather than theoretical possibilities. For our e-commerce system, cybercriminals are the primary threat (high likelihood, financial motivation, proven attack patterns), so investments in web application security and fraud detection deliver the most risk reduction per dollar. Defending equally against all threats would mean spending heavily on APT defenses we'll never face, while under-investing in the credential theft and payment fraud that actually targets e-commerce. Effective security matches defenses to adversaries you'll realistically encounter.
Success Criteria (What "Good" Looks Like)
Your lab is successful if you:
- ✅ Identified assets with clear attacker value (not just "data is valuable")
- ✅ Matched specific threat actor types to specific assets (with justification)
- ✅ Assessed likelihood realistically (not "everyone will attack everything")
- ✅ Prioritized defenses based on threat actor analysis (not arbitrary)
- ✅ Explained why understanding motivation improves defensive efficiency
Extension (For Advanced Students)
If you finish early, explore these questions:
- How would your threat assessment change if your organization went public (IPO)? New threat actors?
- Research one real breach in your chosen industry. What threat actor type? What was their motivation?
- How does "threat intelligence" help defenders prioritize? What sources would you use?
🎯 Hands-On Labs (Free & Essential)
Explore attacker behavior, reconnaissance, and defensive analysis. Complete these labs before moving to reading resources.
🎮 TryHackMe: OSINT Fundamentals
What you'll do: Use open-source intelligence techniques to gather information about
targets, assets, and exposure.
Why it matters: Most attacks start with reconnaissance. Understanding OSINT helps
you think like attackers and reduce exposure.
Time estimate: 1-1.5 hours
🎮 TryHackMe: Phishing Fundamentals
What you'll do: Analyze phishing techniques, pretexts, and social engineering tactics
used by real attackers.
Why it matters: Human-focused attacks remain the most common entry point. Knowing
how they work improves defense.
Time estimate: 1-1.5 hours
🏁 PicoCTF Practice: Forensics (Beginner)
What you'll do: Investigate basic digital artifacts to understand how defenders detect
and analyze attacks.
Why it matters: Defender perspective balances attacker mindset and shows how
attacks are traced.
Time estimate: 1-2 hours
💡 Lab Tip: For each attacker type, write one likely target and one likely technique. This makes threat actor analysis practical.
Resources (Free + Authoritative)
Work through these in order. Focus on attacker behavior and defensive mindset.
📘 MITRE ATT&CK Framework
What to explore: Browse the "Tactics" view (Reconnaissance → Impact). Pick 2-3
tactics and read their techniques.
Why it matters: Real-world attacker playbook based on observed behaviors.
Used globally for threat modeling and detection.
Time estimate: 25 minutes (don't try to memorize — understand the
structure)
🎥 Computerphile - The Psychology of Hacking (Video)
What to watch: Full video on attacker mindset and social engineering.
Why it matters: Technical controls fail when humans are manipulated.
Understanding psychology is essential.
Time estimate: 15 minutes
📘 Verizon Data Breach Investigations Report (DBIR) - Executive Summary
What to read: Latest year's Executive Summary (first 10 pages).
Why it matters: Annual analysis of real breaches — shows what actually
happens (not theoretical attacks). Data-driven threat landscape.
Time estimate: 20 minutes
📘 NIST Cybersecurity Framework - Overview
What to read: Review the five functions (Identify, Protect, Detect, Respond,
Recover) with defender mindset.
Why it matters: Framework for resilience — assumes breach will occur,
focuses on minimizing damage and recovery.
Time estimate: 15 minutes
Tip: Completion and XP persist via localStorage. If progress doesn't update immediately, refresh once.
Weekly Reflection Prompt
Aligned to LO3 (Threat Landscape) and LO4 (Risk Reasoning)
Write 200-300 words answering this prompt:
Explain why understanding attacker motivation is essential for effective defense. Use your Lab 6 threat actor analysis as an example.
In your answer, include:
- How different threat actors (cybercriminals vs nation-states vs insiders) target the same system differently
- Why defending against "all threats equally" wastes resources
- How you prioritized defenses based on realistic threat assessment (likelihood × impact)
- What the "defender's dilemma" means (asymmetry between attackers and defenders)
- Why "assume breach" is a more realistic posture than "prevent all attacks"
What good looks like: You demonstrate understanding that security is adversarial — real people with specific motivations make strategic choices about what to attack and how. You show that effective defense requires matching controls to realistic threats, not defending against everything equally. You explain why resilience (detect + respond + recover) complements prevention.